CALL US: +91-11-46515639/40
To receive a quick quotation and response, please submit your requirement here. (24×7 quote by our Cyber Security Expert)


Empower Your Business with Delhi’s Leading Cyber Risk Security Assessment Experts – Radiant Info Solutions
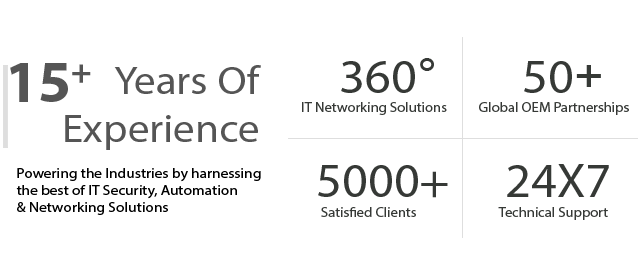
Radiant Info Solutions is a leading Cyber Risk Security Assessments expert company in Delhi, India, providing end-to-end security solutions to help organizations safeguard their critical data, infrastructure, and systems. With a team of experienced cybersecurity professionals, we empower businesses to identify vulnerabilities, assess risks, and implement robust strategies to counter potential cyber threats.
What is a Cyber Risk Security Assessment?
Cyber Risk Security Assessment involves evaluating an organization’s IT ecosystem to identify, analyze, and mitigate potential risks. It enables businesses to enhance their security posture by understanding vulnerabilities and ensuring compliance with industry standards and regulations.
As a trusted Cyber Risk Security Assessments expert company in Delhi, India, Radiant Info Solutions delivers customized assessments to meet the unique requirements of businesses across various industries.
what we offer
Enterprise Cyber Risk Assessment & Exposure Analysis
- Evaluate your complete digital environment—including networks, applications, cloud systems, endpoints, and third-party integrations.
- Identify security gaps, potential threat vectors, policy weaknesses, and high-risk exposure zones across the organization.
- Deliver a cyber risk heat map with prioritized recommendations to minimize vulnerabilities and strengthen resilience.
Threat Modeling, Risk Scoring & Attack Surface Evaluation
- Analyze your organization’s attack surface across internal, external, and cloud-facing assets.
- Identify high-impact risks such as privilege escalation paths, misconfigurations, unpatched systems, and shadow IT.
- Provide a detailed threat model with risk scoring based on likelihood, impact, and mitigation feasibility.
Governance, Policy & Compliance Risk Review
- Assess cybersecurity policies, standards, and governance frameworks aligned with ISO 27001, NIST CSF, SOC 2, and DPDP Act.
- Identify gaps in data privacy, access control, incident response, vendor governance, and security hygiene practices.
- Deliver a compliance roadmap designed to help meet regulatory obligations and audit-readiness requirements.
Technical Risk Assessment & Vulnerability Analysis
- Perform vulnerability scanning and manual validation across infrastructure, cloud instances, applications, and IoT/OT systems.
- Identify critical vulnerabilities, weak controls, insecure configurations, and exploitation opportunities.
- Provide a prioritized remediation plan with hardening guidelines to reduce technical risk exposure.
Business Impact, Incident Readiness & Cyber Resilience Assessment
- Evaluate business processes, critical functions, data flows, and operational dependencies.
- Identify how cyberattacks (ransomware, phishing, insider threats, malware, etc.) could impact business continuity.
- Deliver recommendations for incident response readiness, disaster recovery planning, and operational cyber resilience.
Risk Reporting, Executive Advisory & Continuous Cyber Risk Monitoring
- Provide a comprehensive cyber risk report with categorized risks, severity levels, mitigation timelines, and executive summaries.
- Offer expert-led advisory workshops to guide leadership teams on strategic cyber risk decisions and implementation planning.
- Enable ongoing cyber risk monitoring, periodic reassessments, and maturity improvements for long-term security posture enhancement.
Connect Now, Get Quick Responses!
How it Works

Contact Us
Reach out to our team via phone, email, or our website contact form. Provide some basic information about your business and plans you’re interested in.

Our Team Review the Requirement
Our experts will review your current need and explore the best options to optimize your requirements, ensuring you get the most cost-effective and efficient solution for your business.

Receive Your Customized Quotation
After the review, we will provide you with a detailed, personalized quotation, including pricing and recommendations tailored to your business needs.
Get started today by contacting us, and let’s find the best solution for your business!
Our End to End Cyber Risk & Security Assessment Workflow

1. Engagement Initiation & Risk Context Definition
-
- Alignment with business objectives, risk appetite, and regulatory landscape
- Definition of assessment scope across IT, cloud, applications, and data
- Identification of critical business processes and crown-jewel assets

2.Asset Identification & Digital Footprint Discovery
-
- Comprehensive inventory of infrastructure, applications, and cloud workloads
- Mapping of data flows, trust zones, and external exposure points
- Classification of assets based on sensitivity and business impact

3. Threat Modeling & Attack Surface Analysis
-
- Identification of relevant threat actors, attack vectors, and scenarios
- Analysis of internal and external attack surfaces
- Alignment with current threat intelligence and industry trends

4. Security Control & Maturity Assessment
- Evaluation of administrative, technical, and physical security controls
- Assessment of control effectiveness and maturity levels
- Identification of gaps in people, process, and technology controls

5. Vulnerability & Weakness Assessment
-
- Identification of technical, configuration, and operational weaknesses
- Validation of vulnerabilities through controlled testing techniques
- Prioritization based on exploitability and potential impact

6. Risk Analysis & Business Impact Evaluation
-
- Quantification of cyber risks using likelihood and impact analysis
- Mapping of risks to business processes and compliance obligations
- Prioritized risk register highlighting critical exposures

7. Reporting, Recommendations & Risk Treatment Plan
-
- Detailed assessment report with evidence-based findings
- Actionable remediation and risk treatment recommendations
- Executive-level summary for leadership and decision-makers

8. Validation, Advisory & Continuous Risk Management
-
- Validation of remediation actions and risk reduction effectiveness
- Ongoing advisory for strengthening cyber resilience
- Support for continuous risk assessment and security improvement
Why Partner with Us?
1. Expertise Backed by Industry Standards
Our audits align with global frameworks like ISO 27001, NIST, and CIS. We bring years of hands-on experience across diverse industries to secure your digital infrastructure.
2. Comprehensive Risk Identification
We uncover hidden vulnerabilities across networks, systems, and processes. From penetration testing to policy review, we leave no stone unturned.
3. Actionable, Clear Reporting
We don’t just flag issues — we provide detailed, prioritized action plans. Our reports are easy to understand, even for non-technical stakeholders.
4. Compliance-Driven Approach
Whether it’s GDPR, HIPAA, or local regulatory norms, we ensure you’re audit-ready. Our audits help you avoid fines, reputational risks, and data breaches.
5. Ongoing Support and Remediation Guidance
We stay with you beyond the audit, offering expert advice on fixing the gaps. Think of us as your long-term cybersecurity partner, not just a one-time checker.

Why Radiant Info Solutions for Cyber Risk Security Assessments?
Expert Team: Certified cybersecurity professionals with expertise in advanced risk assessment methodologies.
Customized Solutions: Tailored strategies that align with business objectives and industry standards.
Comprehensive Reporting: Detailed reports with actionable insights and recommendations.
Proven Experience: Trusted by organizations in Delhi and across India for delivering exceptional cybersecurity services.
24/7 Support: Continuous monitoring and assistance to ensure maximum protection.
Modules of Cyber Risk Security Assessments
1. Risk Identification
- Understanding organizational assets and their exposure to potential threats.
- Assessing hardware, software, networks, and data repositories for vulnerabilities.
2. Threat Analysis
- Identifying potential cyber threats, such as malware, phishing, and ransomware attacks.
- Evaluating external and internal threats based on historical and current trends.
3. Vulnerability Assessment
- Conducting manual and automated vulnerability scans.
- Identifying misconfigurations, outdated software, and insecure protocols.
4. Impact Analysis
- Evaluating the potential impact of cyber threats on critical business processes.
- Prioritizing risks based on severity and likelihood.
5. Compliance Assessment
- Ensuring alignment with regulatory requirements such as GDPR, HIPAA, PCI DSS, and ISO 27001.
- Identifying compliance gaps and recommending corrective actions.
6. Business Continuity Planning
- Assessing the organization’s disaster recovery and incident response capabilities.
- Ensuring resilience against cyber incidents with a robust recovery plan.
7. Access Control Evaluation
- Analyzing user access levels and permissions.
- Ensuring proper implementation of role-based access controls (RBAC).
8. Cloud Security Assessment
- Evaluating cloud environments for data security and access control issues.
- Mitigating risks associated with cloud storage, applications, and services.
9. Network Security Assessment
- Identifying open ports, misconfigured firewalls, and insecure network protocols.
- Assessing intrusion detection and prevention systems (IDS/IPS).
10. Social Engineering Risk Assessment
- Identifying human vulnerabilities to phishing and other social engineering tactics.
- Conducting simulated attacks to evaluate awareness and preparedness.
Benefits of Cyber Risk Security Assessments with Radiant Info Solutions
1. Proactive Risk Mitigation
Identify and address vulnerabilities before they are exploited.
2. Enhanced Data Protection
Safeguard sensitive information against unauthorized access and breaches.
3. Regulatory Compliance
Achieve and maintain compliance with industry regulations to avoid penalties.
4. Improved Security Posture
Strengthen overall IT infrastructure with actionable recommendations.
5. Cost Optimization
Prevent costly cyberattacks and ensure business continuity.
6. Customer Confidence
Demonstrate your commitment to cybersecurity, boosting customer trust and loyalty.
Our Cyber Risk Security Assessment Process
Initial Consultation:
Understanding the organization’s objectives and scope of assessment.
Data Collection:
Gathering information about IT infrastructure, applications, and user behavior.
Risk Assessment:
Identifying threats, vulnerabilities, and potential attack vectors.
Evaluation and Analysis:
Analyzing the likelihood and impact of identified risks.
Reporting:
Providing a detailed report with findings, risk levels, and mitigation strategies.
Implementation Assistance:
Assisting in the implementation of recommended security measures.
Continuous Monitoring:
Offering ongoing monitoring and periodic reassessments to ensure sustained protection.
Industries We Serve
Radiant Info Solutions, as a Cyber Risk Security Assessments expert company in Delhi, India, caters to various industries:
- Banking and Finance
- Healthcare
- E-Commerce
- Education
- Retail and Manufacturing
- Government and Public Sector
- Telecommunications
Why Are Cyber Risk Security Assessments Essential?
With the ever-increasing frequency of cyberattacks, businesses must adopt a proactive approach to cybersecurity. Key reasons include:
Identifying Vulnerabilities: Uncover weaknesses in your IT ecosystem.
Preventing Cyberattacks: Reduce the risk of data breaches and downtime.
Ensuring Compliance: Stay aligned with legal and industry-specific regulations.
Safeguarding Reputation: Avoid reputational damage caused by security incidents.
Partner with Radiant Info Solutions Today
As a trusted Cyber Risk Security Assessments expert company in Delhi, India, Radiant Info Solutions is dedicated to protecting your organization from cyber threats. Our customized assessments ensure that your IT infrastructure remains secure, resilient, and compliant with industry standards.
Contact us today to schedule a consultation and take the first step toward robust cybersecurity!
frequently asked questions
What is a Cyber Risk Security Assessment?
A Cyber Risk Security Assessment identifies vulnerabilities, evaluates potential threats, and measures the level of cyber risk to your organization’s systems and data. Radiant Info Solutions provides expert cyber risk assessment consulting services to help businesses build strong defense mechanisms against evolving digital threats.
Why are Cyber Risk Assessments important for businesses?
Cyber risk assessments are vital to detect weaknesses before attackers exploit them. Radiant Info Solutions helps companies evaluate risk exposure, prioritize remediation, and align cybersecurity strategies with business objectives and compliance standards.
What services are included in Radiant’s Cyber Risk Security Assessment?
Radiant offers a comprehensive range of cybersecurity risk assessment services, including:
- Vulnerability Assessment & Penetration Testing (VAPT)
- Network & Endpoint Risk Analysis
- Cloud Security Assessment
- Compliance Gap Analysis (ISO 27001, SOC 2, GDPR)
- Incident Response Readiness
- Cyber Maturity Evaluation
What makes Radiant Info Solutions a leading cyber risk consulting company?
Radiant Info Solutions stands out as a cybersecurity consulting company with certified experts, advanced risk assessment tools, and customized security frameworks. Radiant helps enterprises proactively identify, analyze, and mitigate cyber threats with precision and transparency.
How does Radiant conduct a Cyber Risk Assessment?
Radiant follows a systematic five-step process:
- Asset Identification & Classification
- Threat & Vulnerability Evaluation
- Risk Quantification & Impact Analysis
- Mitigation Planning
- Reporting & Continuous Monitoring
This ensures a complete understanding of your cyber risk posture and actionable recommendations.
How often should an organization perform a Cyber Risk Assessment?
It is recommended to conduct a cyber risk assessment annually or after any significant IT or infrastructure changes. Radiant Info Solutions offers periodic and on-demand risk assessments to ensure your defenses remain effective year-round.
What industries benefit most from Cyber Risk Assessments?
Industries such as banking, healthcare, manufacturing, retail, government, and IT services benefit greatly from cybersecurity risk assessments by Radiant Info Solutions, ensuring compliance, data protection, and operational resilience.
How does Radiant ensure the confidentiality of patient data during testing?
Industries such as banking, healthcare, manufacturing, retail, government, and IT services benefit greatly from cybersecurity risk assessments by Radiant Info Solutions, ensuring compliance, data protection, and operational resilience.
How does Radiant help reduce cyber risk exposure?
Radiant’s experts identify high-risk areas, recommend mitigation strategies, and implement proactive security measures to minimize exposure. The company provides continuous monitoring, employee awareness training, and incident response consulting for end-to-end protection.
What compliance standards does Radiant align with during assessments?
Radiant ensures compliance with international standards including ISO 27001, GDPR, HIPAA, PCI DSS, and SOC 2. The company’s cyber risk consulting services help businesses meet regulatory and audit requirements efficiently.
Does Radiant provide remediation and post-assessment support?
Yes. Radiant offers end-to-end remediation consulting, ensuring all identified vulnerabilities are addressed and verified. Post-assessment services include retesting, policy updates, and security framework optimization for continuous improvement.
What are the benefits of partnering with Radiant for cyber risk assessment services?
Partnering with Radiant Info Solutions ensures:
- Certified cybersecurity consultants
- Comprehensive risk identification and mitigation
- Custom-tailored assessment frameworks
- Regulatory compliance and audit readiness
- Enhanced cyber resilience and business continuity
Why Choose Radiant as Your Preferred Cybersecurity Partner?
Radiant Info Solutions is your trusted partner for cybersecurity, delivering end-to-end protection and expert guidance. We help businesses safeguard critical data with advanced, tailored solutions. Partner with us for reliable, proactive, and scalable cybersecurity support that keeps your organization secure.
Message for Quick Quotation
For a quick quotation, share your requirements here:
![]()
Looking for Advice ?
Connect with our Cybersecurity Consultant
📞 +91-11-46515639/40
📧 leads@radiant.in








