CALL US: +91-11-46515639/40
To receive a quick quotation and response, please submit your requirement here. (24×7 quote by our Cyber Security Expert)


Secure Your Future: Comprehensive Web Application Vulnerability Assessment and Penetration Testing with Radiant Info Solutions
In today’s digital-first economy, web applications are at the core of business operations — from e-commerce to enterprise portals and SaaS platforms. However, with this increased dependency comes higher exposure to cyber threats. Radiant Info Solutions, a leading web application WAVAPT (Web Application Vulnerability Assessment and Penetration Testing) service provider company in India, empowers businesses to identify, assess, and eliminate web security vulnerabilities before they can be exploited.
Our WAVAPT services combine automated vulnerability scanning and manual penetration testing to deliver a deep, realistic, and actionable evaluation of your web applications’ security posture.
As cyberattacks evolve, Radiant ensures your business remains one step ahead — protecting your digital ecosystem, customers, and brand reputation through expert web application vulnerability assessment and penetration testing solutions.
what we offer
Comprehensive Web Application Vulnerability Assessment (WA-VAPT)
- Evaluate your complete web application ecosystem—including front-end, back-end, APIs, and database layers.
- Identify vulnerabilities related to authentication, authorization, input validation, configuration, and data exposure.
- Deliver a detailed WA-VAPT score with prioritized recommendations to strengthen your application security posture.
OWASP Top 10–Aligned Penetration Testing
- Conduct deep-dive penetration testing aligned with OWASP Top 10, including injection flaws, XSS, CSRF, broken access control, and insecure deserialization.
- Simulate real-world attack scenarios to identify exploitation possibilities and business logic manipulation risks.
- Provide actionable insights with technical guidance to fix critical vulnerabilities effectively.
API & Backend Logic Security Testing
- Evaluate REST, SOAP, and GraphQL APIs for broken access control, weak authentication, insecure endpoints, and IDOR risks.
- Analyze backend workflows, database queries, error handling, and business logic for potential abuse and data tampering.
- Deliver a complete API security posture assessment with remediation recommendations.
Configuration, Deployment & Server Security Review
- Assess application hosting environments, middleware, servers, and deployment pipelines for security misconfigurations.
- Identify risks such as insecure headers, outdated libraries, weak SSL/HTTPS configurations, and exposed admin panels.
- Recommend secure deployment practices, configuration hardening, and DevSecOps-based enhancements.
Secure Code Review & Application Architecture Analysis
- Perform manual and automated review of source code to detect insecure coding patterns, unsafe functions, and potential logic flaws.
- Analyze application architecture, data flow, session management, and encryption usage for structural weaknesses.
- Provide developers with best-practice coding guidelines and architecture improvement strategies.
Final Reporting, Remediation Support & Re-Validation Testing
- Provide a comprehensive WA-VAPT report with severity ranking, exploitation proof, and step-by-step remediation guidance.
- Offer expert consulting sessions to help your development and security teams implement recommended fixes correctly.
- Conduct retesting and verification to ensure all vulnerabilities are resolved and the application is secure for deployment.
Connect Now, Get Quick Responses!
How it Works

Contact Us
Reach out to our team via phone, email, or our website contact form. Provide some basic information about your business and plans you’re interested in.

Our Team Review the Requirement
Our experts will review your current need and explore the best options to optimize your requirements, ensuring you get the most cost-effective and efficient solution for your business.

Receive Your Customized Quotation
After the review, we will provide you with a detailed, personalized quotation, including pricing and recommendations tailored to your business needs.
Get started today by contacting us, and let’s find the best solution for your business!
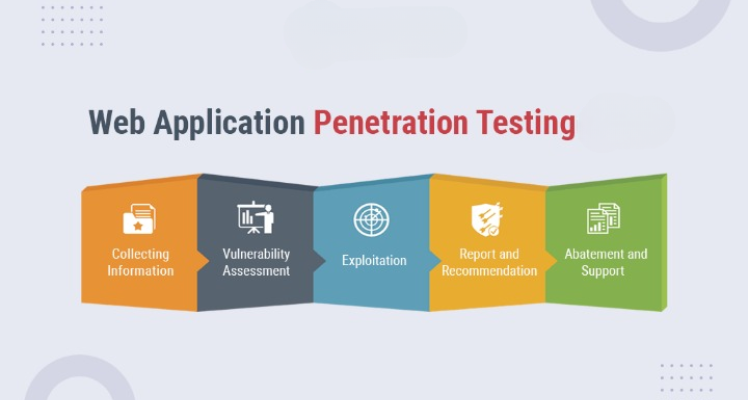
Our End to End Deployment Workflow – Web Application VAPT (WAVAPT)

1. Scope Definition & Security Consultation
- Understanding application architecture, business logic, and data sensitivity
- Defining in-scope URLs, APIs, modules, and environments (prod/UAT/dev)
- Selection of black-box, grey-box, or white-box testing approach

2. Pre-Engagement Planning & Authorization
- Rules of engagement, testing windows, and approval sign-off
- User roles, credentials, and access setup (if applicable)
- Risk mitigation planning to avoid service disruption

3. Application Discovery & Mapping
- Identification of entry points, parameters, and user flows
- Authentication, session management, and role mapping
- API and third-party integration discovery

4. Vulnerability Assessment (Automated & Manual)
- Scanning for OWASP Top 10 vulnerabilities
- Manual validation to eliminate false positives
- Severity classification based on impact and exploitability

5. Penetration Testing & Exploitation
- Controlled exploitation of confirmed vulnerabilities
- Testing of business logic flaws and access control issues
- Validation of real-world attack scenarios

6. Risk Analysis & Compliance Mapping
- Business impact analysis of identified risks
- Mapping findings to OWASP, CERT-In, ISO 27001, and PCI-DSS (if applicable)
- Prioritization of remediation actions

7. Reporting & Stakeholder Presentation
- Detailed technical report with proof of concept (PoC) evidence
- Executive summary for management and auditors
- Clear remediation steps and best-practice recommendations

8. Remediation Support & Re-Testing
- Advisory support during vulnerability remediation
- Re-testing to validate fixes and closure
- Continuous improvement and security hardening guidance
Why Partner with Us?
1. Expertise Backed by Industry Standards
Our audits align with global frameworks like ISO 27001, NIST, and CIS. We bring years of hands-on experience across diverse industries to secure your digital infrastructure.
2. Comprehensive Risk Identification
We uncover hidden vulnerabilities across networks, systems, and processes. From penetration testing to policy review, we leave no stone unturned.
3. Actionable, Clear Reporting
We don’t just flag issues — we provide detailed, prioritized action plans. Our reports are easy to understand, even for non-technical stakeholders.
4. Compliance-Driven Approach
Whether it’s GDPR, HIPAA, or local regulatory norms, we ensure you’re audit-ready. Our audits help you avoid fines, reputational risks, and data breaches.
5. Ongoing Support and Remediation Guidance
We stay with you beyond the audit, offering expert advice on fixing the gaps. Think of us as your long-term cybersecurity partner, not just a one-time checker.

What is WAVAPT?
WAVAPT (Web Application Vulnerability Assessment and Penetration Testing) is a dual-phase security process designed to detect and exploit vulnerabilities within your web applications.
- Vulnerability Assessment: Identifies potential flaws in your application architecture, coding, and configuration.
- Penetration Testing: Simulates real-world attacks to verify the exploitability and business impact of discovered vulnerabilities.
By integrating both approaches, Radiant’s WAVAPT service delivers comprehensive visibility into your web application’s security posture — ensuring no hidden risks remain undetected.
Radiant Info Solutions’ Methodology
At Radiant Info Solutions, our web application vulnerability assessment and penetration testing methodology is built on international standards such as OWASP Top 10, ISO 27001, and NIST.
- Information Gathering
We start by collecting data about your web application’s structure, technology stack, and endpoints. This helps map out the attack surface.
- Vulnerability Scanning
Our experts conduct automated scans to detect known vulnerabilities like injection flaws, insecure configurations, and outdated software.
- Manual Penetration Testing
Certified testers perform in-depth manual analysis to exploit and validate identified vulnerabilities, uncovering risks often missed by automated tools.
- Risk Evaluation
Each vulnerability is classified by severity, exploitability, and business impact, ensuring you can prioritize remediation effectively.
- Detailed Reporting
Radiant provides a detailed report with step-by-step findings, evidence, and practical recommendations for patching vulnerabilities.
- Retesting
After remediation, we re-evaluate your application to confirm that all identified vulnerabilities have been securely fixed.
Benefits of Web Application WAVAPT Testing
Partnering with Radiant Info Solutions, a certified WAVAPT and penetration testing company, ensures multiple strategic and operational benefits:
- Comprehensive Web Security: Identify vulnerabilities in application logic, APIs, and authentication systems.
- Compliance Readiness: Align with security standards like OWASP, ISO 27001, PCI DSS, SOC 2, and GDPR.
- Risk Mitigation: Prevent data breaches, unauthorized access, and service disruptions.
- Business Continuity: Minimize downtime and financial loss due to cyberattacks.
- Customer Trust: Strengthen your organization’s reputation by safeguarding customer data and digital assets.
Radiant’s web application vulnerability assessment and penetration testing services ensure your applications are secure, compliant, and resilient.
Why Choose Radiant Info Solutions?
As a trusted web application WAVAPT service provider company in India, Radiant Info Solutions is recognized for its expertise, precision, and commitment to client success.
- Certified Security Experts
Our team comprises CEH (Certified Ethical Hackers) and CISSP-certified professionals with years of hands-on experience in web application testing.
- Comprehensive Security Coverage
We offer end-to-end testing for web, mobile, and API-based applications, ensuring every digital layer is protected.
- Advanced Tools and Techniques
We utilize industry-standard tools combined with expert manual analysis to uncover hidden threats across your application environment.
- Transparent Reporting
Every engagement includes detailed findings, proof-of-concept exploit evidence, and clear remediation guidance to enhance your internal security.
- Industry Recognition
Radiant Info Solutions is a trusted cybersecurity vendor and preferred WAVAPT testing partner for enterprises across BFSI, IT, Healthcare, and E-commerce sectors.
- Customer-Centric Approach
We believe in collaboration and clarity. Radiant works closely with your IT teams to implement corrective measures and strengthen your long-term security posture.
Radiant’s Edge in Web Application Security
What sets Radiant Info Solutions apart is its ability to merge technical depth with practical business understanding.
Our web application vulnerability assessment and penetration testing services not only detect flaws but also provide risk-based insights that help organizations prioritize actions based on critical impact.
Whether you operate a large enterprise or a growing startup, our WAVAPT testing solutions are scalable, customizable, and aligned with your operational and compliance goals.
Cybersecurity begins at the application layer — where most attacks originate. Radiant Info Solutions, a leader in web application WAVAPT vulnerability assessment and penetration testing, ensures your business applications are secure, compliant, and resilient against modern cyber threats.
With a blend of cutting-edge tools, certified professionals, and industry best practices, Radiant delivers end-to-end protection for your web applications, APIs, and digital interfaces.
Choose Radiant Info Solutions — your trusted partner for WAVAPT and web application security services in India. Strengthen your digital defense and stay secure in an ever-evolving cyber landscape.
Why Choose Radiant as Your Preferred Cybersecurity Partner?
Radiant Info Solutions is your trusted partner for cybersecurity, delivering end-to-end protection and expert guidance. We help businesses safeguard critical data with advanced, tailored solutions. Partner with us for reliable, proactive, and scalable cybersecurity support that keeps your organization secure.
Message for Quick Quotation
For a quick quotation, share your requirements here:
![]()
Looking for Advice ?
Connect with our Cybersecurity Consultant
📞 +91-11-46515639/40
📧 leads@radiant.in
frequently asked questions
What is Web Application VAPT?
Web Application Vulnerability Assessment and Penetration Testing (WA-VAPT) is a security testing process that identifies vulnerabilities in web applications, APIs, and associated services. It helps organizations prevent cyber threats by assessing and mitigating security risks.
Why is WA-VAPT important for businesses?
WA-VAPT is crucial because:
- Web applications are frequent targets for cyberattacks
- Prevents SQL injection, XSS, CSRF, and other web-based threats
- Helps in compliance with security standards like OWASP, PCI-DSS, and GDPR
- Protects sensitive customer and business data from hackers
What is the difference between Web Vulnerability Assessment and Penetration Testing?
- Vulnerability Assessment – Identifies potential security gaps using automated scans.
- Penetration Testing – Manually simulates cyberattacks to exploit vulnerabilities and assess their impact.
What are the common threats identified in WA-VAPT?
- SQL Injection (SQLi) – Attackers manipulate database queries
- Cross-Site Scripting (XSS) – Malicious scripts execute in user browsers
- Cross-Site Request Forgery (CSRF) – Unauthorized actions performed on behalf of users
- Broken Authentication & Session Management – Weak login mechanisms exploited
- Security Misconfigurations – Improper settings that expose vulnerabilities
How does Radiant Info Solutions perform WA-VAPT?
Radiant Info Solutions follows a systematic approach:
- Reconnaissance & Information Gathering – Identifying exposed data and entry points
- Automated Vulnerability Scanning – Using security tools to detect risks
- Manual Penetration Testing – Simulating real-world attacks
- Risk Assessment & Reporting – Prioritizing vulnerabilities by severity
- Remediation & Security Hardening – Providing recommendations and fixes
How often should businesses conduct WA-VAPT?
Web applications should be tested:
- Before launching a new application
- After significant updates or feature changes
- At least once a year to ensure continuous security
How does WA-VAPT help in regulatory compliance?
WA-VAPT ensures adherence to security standards such as:
- OWASP Top 10 – Industry-recognized web security best practices
- PCI-DSS – Securing payment transactions
- ISO 27001 – Information security management compliance
- GDPR – Data protection and privacy laws
Why choose Radiant Info Solutions for WA-VAPT?
Radiant Info Solutions offers:
- Certified Security Experts – Skilled in ethical hacking and cybersecurity
- Comprehensive Web Testing – Covering all application layers
- Actionable Security Reports – Providing detailed vulnerability insights
- Post-Fix Verification – Ensuring security patches are effective
What deliverables will I receive from Radiant Info Solutions?
- Detailed Security Report – Identified vulnerabilities and risk ratings
- Attack Simulation Summary – How hackers could exploit weak points
- Remediation Guidance – Steps to secure web applications
- Post-Remediation Testing – Verifying applied security measures